| « back Browsing Levels: #2402 "block cipher" | |
| prev: #2401 "Memoryless Hole?" | next: #2403 "war of the bots...thats how we roll." |
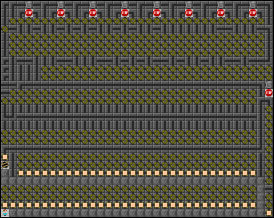
"block cipher" by pieguy |
|
| ||||||||||||||||||
| Comments (turn spoilers on) | ||||
| 14239 | block cipher | Eric119 (921) | Wed 11 Aug 2010 20:08 | |
| Hahahaha, I have the solution to this level. | ||||
| 12593 | block cipher | gary (1998) | Tue 08 Sep 2009 23:39 | |
| ...but wait, people may use the "THIS IS NOT POSSIBLE!!!" comment on this level, because people may find that this is "impossible". | ||||
| 12592 | block cipher | gary (1998) | Tue 08 Sep 2009 23:36 | |
| Well, beginners in Escape usually play the "Very funny." directory and play the ones which are too easy for them... And they rate them without playing. | ||||
| 12591 | block cipher | radiant (1469) | Tue 08 Sep 2009 23:16 | |
| I guess I won't need to release my solution key level then. Speaking of which, who was the most recent rater here, who put up a 9 in difficulty? |
||||
| 12589 | block cipher | Tom 7 (1) | Tue 08 Sep 2009 22:54 | |
| By request. It's a fantastic creation but maybe a bit cruel to have it in the main collection. Radiant, very impressive. |
||||
| 12588 | block cipher | Tom 7 (1) | Tue 08 Sep 2009 22:52 | |
| (admin) Moved to triage/veryfunny. | ||||
| 12484 | block cipher | radiant (1469) | Tue 01 Sep 2009 00:03 | |
| Maybe if it were actually spoiling anything, instead of vaguely discussing the construction of the level. If one of us were just going to state the key sequence, clearly that gets a spoiler. But other than that, is anyone really going to take these bits and pieces and get the second solve time down from 6 months? (If you are, good for you.) Besides, even if the outcome of my non-poll is to reveal the sequence, it won't be by way of comment. |
||||
| 12483 | block cipher | John Lewis (411) | Mon 31 Aug 2009 23:06 | |
| Um, excuse me, gentlemen...but shouldn't these comments be marked as spoilers? :) | ||||
| 12480 | block cipher | pieguy (511) | Mon 31 Aug 2009 20:33 | |
| i believe solutions are automatically optimized before upload, so any back-and-forth running would have been taken out. plus, that still would have revealed the parity of the bits in the key. it's not much, but when you want a cryptosystem to be secure, any leak of information is bad. your extra row idea would be great if you wanted to do a hash instead of a cipher. as far as i know decrypitng 0 isn't any easier than decrypting a random plaintext (but then again, i thought it would take a million years to solve this, so what do i know?) |
||||
| 12479 | block cipher | radiant (1469) | Mon 31 Aug 2009 20:09 | |
| I checked the original solution and it was the same as what I found. Whether there are any other solutions or not, I stand by a 10-6-9 rating because to me "rigidity 10" means only one successful possibility at every move, and at the least it's possible to run backwards here before processing the cipher. Even if you didn't use the neat broken block mechanism, you could have run back and forth in place to delay the solution to 1142, and been nearly as effective at disguising the bit count. Probably even more effective at getting people to try a bunch of guesses before they gave up. | ||||
| 12478 | block cipher | pieguy (511) | Mon 31 Aug 2009 19:41 | |
| i'm mostly curious if the key you found was the same as the one in the original solution (someone gave it a rigidity of 9). was it your ideas from your april comment that ultimately led to the solution? | ||||
| 12477 | block cipher | radiant (1469) | Mon 31 Aug 2009 19:34 | |
| If you really wanted to be funny, you could have added another row or two of remotes along the top and had a bot there to flip some bits of the text after step 1008, so as not to be constrained by designing to a single predetermined plaintext. Just enter in your key of choice, run the cipher to see how it turns out, then put in the requisite bit flips after the fact. How about I take a poll on whether I disclose the key to finally put this level to rest, or keep it as a challenge for anyone who dares to follow...then just ignore the results and replace it with a roll of a 30-sided die. Sure I could just use a coin, but bigger numbers and more complexity are good, right? |
||||
| 12476 | block cipher | pieguy (511) | Mon 31 Aug 2009 19:13 | |
| holy cow! you actually solved it?!?! i'm impressed. how about a breakdown of cpu time/memory usage? tom, would it be appropriate to move this level into "very funny" or something similar? i should have asked for this sooner. |
||||
| 12467 | block cipher | radiant (1469) | Tue 25 Aug 2009 05:47 | |
| Well, that takes care of that. | ||||
| 12153 | block cipher | radiant (1469) | Thu 09 Apr 2009 13:52 | |
| Let's try thinking about this level in terms of "What does it take to construct it?" Changing the initial text makes a significant difference in the number of times each bit is flipped over the course of the cipher, and this certainly isn't a symmetric cipher, so a chosen key and ending text don't give a very easy path to finding the initial text needed. Brute-forcing the text just gets you into a search space twice as big as trying to brute force the key. We might have luck trying to look at the function from the perspective of "What are the valid predecessors of 0x0000000000000000?" and, while it may not be feasible to expand the search tree out to the full 1008 (effectively 1007) depth, we might at least be able to eliminate a few of the bits as dead ends. |
||||
| 11829 | block cipher | Tom 7 (1) | Sat 07 Mar 2009 09:23 | |
| Very nice. Now I can take DES off my level to-do list. :) | ||||
| 11824 | block cipher | wowei (685) | Sat 07 Mar 2009 08:17 | |
| hey this looks like a well designed crypt-machine. i especially like the way the number of bits is disguised when entering the key; perhaps a bit paranoid but nice and funny too. but i dont think, it gives very strong encryption. it reminds of DES with a 63 bit key and 24 bit salt or 7 s-boxes and going for 16 rounds. but the resamblence ends herewith, i think. DES uses the same function for cryption and decryption only with its subkeys in opposite order from round to roind. and there doesnt exist an inverted function. means: (i=input or cleartext, k=key, o=output or cipher) fik(i, k) -> o doesnt have an inversion fok(o, k) -> i it seems very likely that an inverted function (fok) exists in your machine. and that weakens the strength of cryption and gives a point for attacking it. it even increases the probability of the existence of fio(i, o) -> k which would ruin the crytion. Nevertheless i dont believe, i will be able to solve this puzzle, and thatswhy i hate your machine! ;) brute force, hahaha. dont you people think before writing? does your key contain any message at least, pieguy? |
||||
| 11788 | block cipher | pieguy (511) | Sat 28 Feb 2009 05:11 | |
| cracking DES in less than a day was the result of the coordination of thousands of computers (including one built specifically for cracking DES), which enabled them to check 200 billion keys per second. so far the best i've been able to achieve for this cipher is 80k keys per second (per core) on my computer, meaning it would take an expected million cpu years for my computer to crack it. | ||||
| 11782 | block cipher | gary (1998) | Fri 27 Feb 2009 05:30 | |
| I think that it may be not solved in 24 hours, but it can be solved about 100 to 200 days. | ||||
| 11781 | block cipher | radiant (1469) | Fri 27 Feb 2009 03:03 | |
| Unsolvable? In a world where DES can be brute-forced in what, 24 hours? | ||||
| 11780 | block cipher | pieguy (511) | Fri 27 Feb 2009 00:49 | |
| 'block cipher' uploaded by pieguy: probably unsolvable... |
||||